Recent News & Insights
Providing a reliable activation process, KMS Activator stands as an efficient tool for various Microsoft Windows and Office versions.
Activator for Windows&Office Kmsautofree
Library z-libData Recovery and Business Continuity in the Event of a Disaster
When a disaster or system failure disrupts your business, data loss can be a major — and a costly — consequence. And yet [...]
How to Create Your IT Disaster Recovery Plan
When it comes to an IT disaster striking your business, the term to use is probably “when,” not “if.” And when a disaster [...]
Stay Safe and Productive in 2021: 3 Phishing Threats to Know for the New Year
Cybercriminals are always evolving their methods of getting unauthorized access to your private information and with the rapid, on-a-dime increase of the remote workforce, [...]
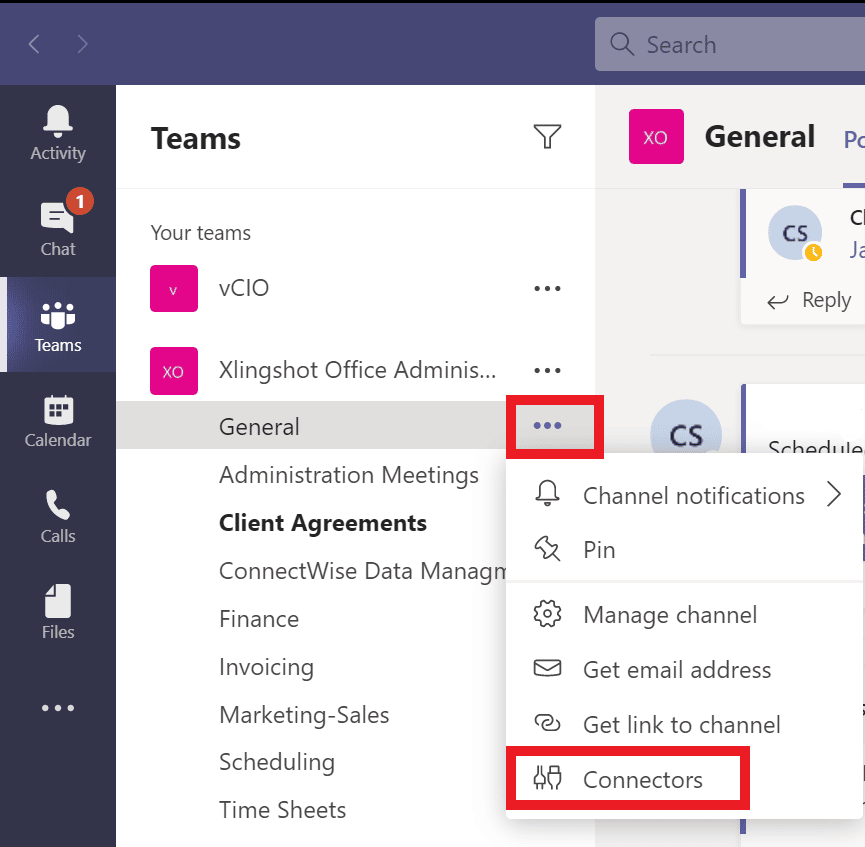
How to Add a Connector to an MS Teams Channel
Connectors in MS Teams are a very useful function but few users know about them. You can use connectors to sync updates and data [...]
How Cloud Services Can Ensure You Make the Most of Your Investment
How Cloud Services Can Ensure You Make the Most of Your Investment There are solid financial and operational reasons to be in the [...]
Smishing: What is it and How To Avoid Being a Victim?
What is Smishing? Smishing is a type of phishing attack but instead of arriving by email, as phishing attacks generally do, they come via [...]
Managing Risk with a Cloud Migration Checklist
The cloud is a wonderful place to be for many businesses, and there are good reasons so many are adopting the cloud: cost-effectiveness, [...]
Private Cloud vs. Public Cloud: Everything You Need to Know
In these days of remote work, moving to the cloud has surfaced as an urgent business imperative for the C-suite. And it makes [...]
Enabling Remote Workers With Your Cloud Infrastructure
If your business is like so many others, you’ve probably experienced a massive surge in your team members having to work remotely, especially [...]
Microsoft Teams 101: Tabs in Microsoft Teams
Tabs in Microsoft Teams With tabs, you and your team members can access apps and content within a chat or channel. This makes it [...]
What Does Outsourced IT Support Even Do?
Considering outsourcing your IT support, but not quite sure what services are covered or what an engagement with an outside IT provider would [...]
Is Shadow IT a Problem at Your Business?
The term “shadow IT’ sounds pretty nefarious, and the activities around it certainly can be. But oftentimes it’s a result of company employees [...]
Why Network Monitoring Around the Clock Matters
Are your networks healthy? How would you know if they were, or if their health were to become compromised? Or do you just [...]
Network Security Monitoring vs. Network Monitoring: What’s the Difference?
In a previous post, we talked about the importance of network monitoring around the clock, with an emphasis on monitoring all the various [...]
Choosing a Cybersecurity Service Provider
Don’t have the budget for an in-house cybersecurity specialist? No worries. You can still get access to the expertise you need to reduce [...]
How to Recognize a Phishing Attempt
Phishing is a type of social engineering used to steal and collect data like login credentials, credit card, and bank account numbers, and other [...]
Why Your Small Business Needs an IT Services Company
We know how it goes: You must be fully focused on running your business, not the technology that your business runs on. If [...]
AccountabilIT Named One of the World’s Top MSSPs
What does it take to be one of the world’s top managed security service providers (MSSPs)? We’ve got it. Find out why it [...]
Getting Your IT Solutions to Work for You
I don’t want to think about it, I just want it to work. We get it. On the day of incorporation, back when you [...]
When it Comes to Phishing, Email Subjects are “Red Herrings”
Unfortunately, email phishing and other types of cybercrime have gone up significantly during the Coronavirus pandemic. The surge in working from home has left [...]
Data Breaches: What Small and Medium Businesses Need to Know
What is a Data Breach? A data breach is simply when information is accessed without authorization. This can be banking information, health, and other [...]
Creative Ways to Boost Employee Morale While Working from Home
Working from home is the new norm for many of us. Keep reading for easy ideas and accessible tools for boosting team morale and [...]
Cloud backup or cloud storage? Find the right solution for your business.
As coronavirus continues to evolve and spread, many companies and organizations are looking at long-term solutions for working from home. One of the most [...]
The Top 2 Must-Know Skills for Microsoft Teams: Hosting Virtual Meetings and Screen Sharing
The global pandemic era has forced most organizations to rely on virtual meetings and other remote collaboration tools to carry on with operations. With [...]
-
Data Loss Prevention (DLP) with Microsoft Sentinel and Microsoft DefenderDecember 1st, 2023
-
App Governance in Microsoft Defender for CloudNovember 19th, 2023
-
The CISO’s Guide to Balancing Security and ProductivityOctober 23rd, 2023
-
The Role of Collaboration in Cybersecurity SuccessOctober 12th, 2023